A recent announcement from Google has raised alarms within the Bitcoin and cryptocurrency sectors, indicating that the timeline for preparing against quantum computing threats may be far shorter than initially anticipated. In a whitepaper released on March 31, researchers from Google Quantum AI revealed that breaking the elliptic curve cryptography that secures Bitcoin, Ether, and numerous major cryptocurrencies could potentially require fewer than 500,000 physical qubits on a superconducting quantum computer. This figure is a significant reduction from earlier estimates, which suggested the number could be in the millions.
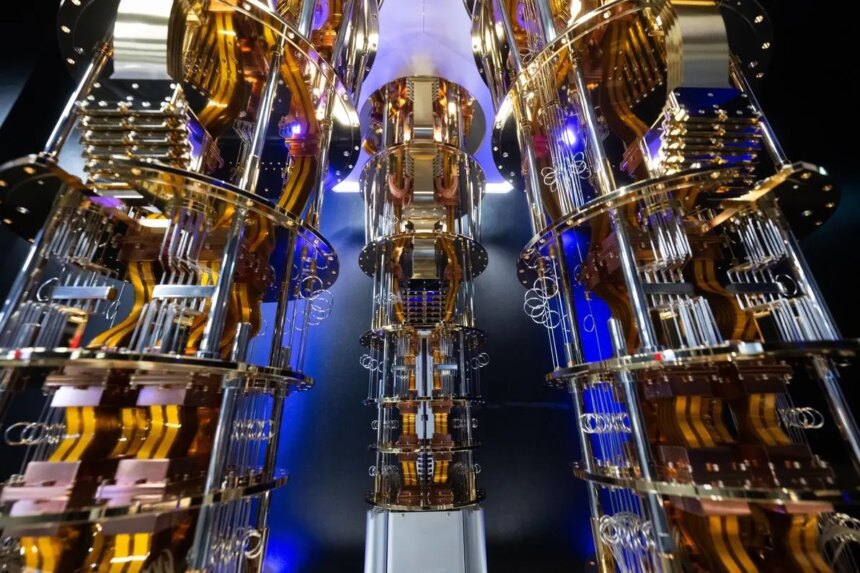
The whitepaper boasts prominent contributors, including Justin Drake from the Ethereum Foundation and Dan Boneh from Stanford University, alongside a team of Google Quantum AI researchers. Notably, the paper mentions that prior to its publication, Google engaged with U.S. government officials and collaborated with various institutions, including Coinbase and the Stanford Institute for Blockchain Research. Despite the ominous implications of the research findings, it’s important to note that no existing quantum computer can currently execute this type of attack. Google’s most advanced chip, Willow, possesses just 105 qubits.
Drake expressed heightened confidence in the potential for a quantum computer to recover a private key from an exposed public key by 2032, suggesting a minimum 10% chance of such an event occurring by that year. The reliability of Bitcoin’s security hinges on a mathematical principle that renders it computationally impossible for classical computers to derive a private key from a public key, which is rooted in the Elliptic Curve Discrete Logarithm Problem (ECDLP). Traditional computers would require an impractically lengthy period, exceeding the age of the universe, to decipher this cryptographic connection.
Quantum computers, however, stand to upend this assumption dramatically. An algorithm developed by mathematician Peter Shor in 1994 can solve the ECDLP significantly faster than any classical method. A quantum computer equipped with sufficient stable and error-corrected qubits operating Shor’s algorithm could efficiently recover a private key, forge a digital signature, and subsequently drain a wallet’s funds. Interestingly, while this quantum threat could endanger Bitcoin’s digital signature schemes, it would not affect its proof-of-work mining process, which employs the SHA-256 hash function.
The research classified three types of quantum attacks on cryptocurrencies: on-spend, at-rest, and on-setup attacks. On-spend attacks target transactions in transit, exploiting the moment when a Bitcoin transaction is broadcast and the public key is exposed. Attackers could derive private keys in an estimated nine minutes, using precomputation techniques. Ethereum and Solana, with shorter confirmation times, might face heightened risks as well, despite some inherent defenses against rapid attacks.
At-rest attacks affect dormant wallets and public keys already exposed on the blockchain, with the potential timeframe for exploitation extending days or weeks. Meanwhile, on-setup attacks represent targeted vulnerabilities in fixed protocol parameters, which could create reusable backdoors. However, Bitcoin remains insulated from this particular threat, while Ethereum’s protocol mechanisms could be at risk.
The team outlined two quantum circuits executing Shor’s algorithm tailored for the secp256k1 elliptic curve, with estimates requiring fewer than 1,200 to 1,450 logical qubits to effectively perform an attack. More aggressive hardware assumptions could yield estimates under 100,000 physical qubits, though achieving these designs remains unproven in real-world devices. Google’s use of zero-knowledge proof technology to validate these findings adds an innovative layer of secrecy and robustness to their claims.
In response to emerging quantum threats, the Ethereum community has been proactive, establishing a dedicated hub for post-quantum security and aiming for a complete transition to quantum-resistant protocols by 2029. In contrast, Bitcoin’s approach has been less coordinated, highlighted by the recent integration of a new output type that offers no immediate quantum-resistance but lays the groundwork for future proposals.
For cryptocurrency users concerned about quantum vulnerabilities, there are actionable steps to mitigate risks. Users should avoid reusing address types that expose public keys, transfer funds from previously used addresses to fresh ones, and remain vigilant for post-quantum compatibility in wallets, exchanges, and custody services. While immediate threats may not loom large, the time to act is indeed upon the cryptocurrency community to prepare for a changing technological landscape.